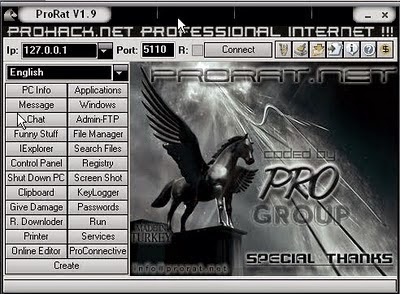
ProRat is one of the best Remote Administration Tool which can be used to easily hack any system and there are other features described below..
***** Do at your own risk ****
To be honest if you successfully can social engineer you victim and make him install the the prorat's server then you can completely control the victim and you can do the features available to do in ProRat. Below I will tell you how to install it and use it..
Step 1 : Download it from the Link below and Install it from ProRat.exe
Step 2 : After you Install it Open up the program and You should see the following window.
Step 3 : Click on the "Create" button in the bottom. Choose "Create ProRat Server".
Step 4 : Next put your IP address so the server could connect to you. You need not enter your IP address manually, you can do this by just clicking on the little arrow. it automatically fills your IP address.
Next put in your e-mail so that when and if a victim gets infected it will send you an email.
Step 5 : Now Open General settings. This tab is the most important tab. In the check boxes, we will choose the server port the program will connect through, the password you will be asked to enter when the victim is infected and you wish to connect with them, and the victim name. As you can see ProRat has the ability to disable the windows firewall and hide itself from being displayed in the task manager. Just follow the steps as shown in the figure.
Step 6 : Click on the Bind with File button to continue. Here you will have the option to bind the trojan server file with another file. You can select an image, text file or pdf file, So as to make the victim trust your file.
Step 7 : Click on the Server Extensions button to continue. Here you choose what kind of server file to generate. I prefer using .exe files.
Step 8 : Click on Server Icon to continue. Here you will choose an icon for your server file to have. The icons help mask what the file actually is.
Step 9 : After this, press Create server, your server will be in the same folder as ProRat. Start giving this file to your victim. When the victim double click the file, his computer will be in your control.
Step 10 : Now the hacker has lot of options to choose from. He can do many funny things with the victim’s computer and even serious things too ;).








but he need his ip to hack
ReplyDelete